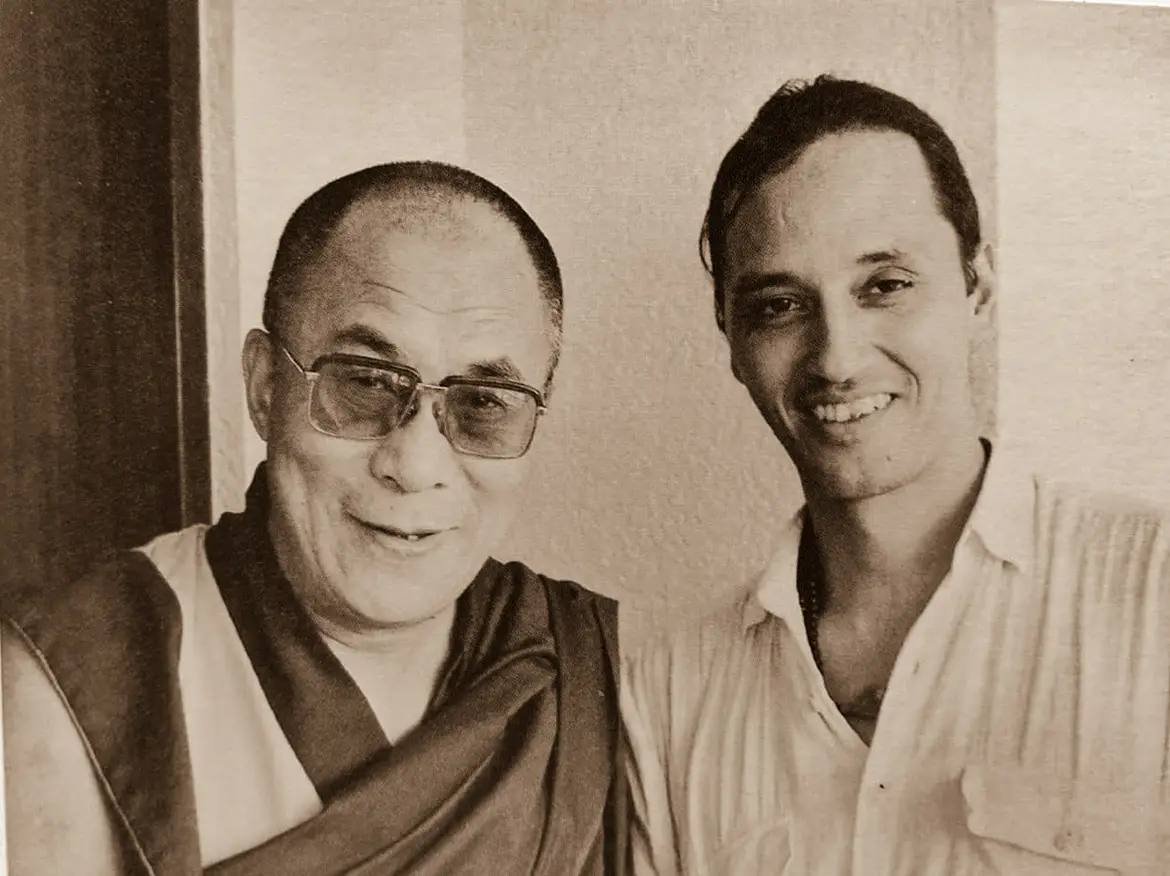
Limited Edition Prints
The images include archival prints from my analogue work – the ones from Memories of the Sacred book and select older images. Also included are images of my digital collection
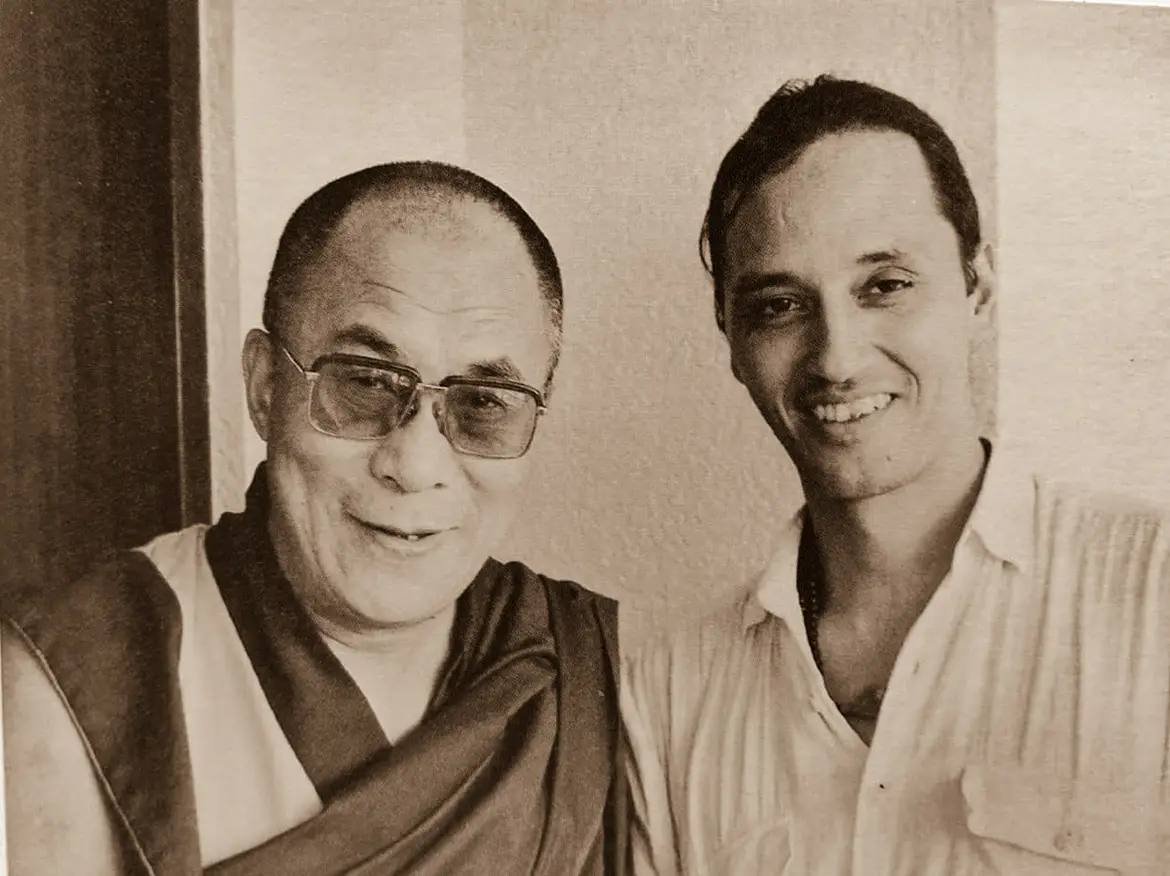
The images include archival prints from my analogue work – the ones from Memories of the Sacred book and select older images. Also included are images of my digital collection